Search posts by keywords:
Filter posts by author:
Related Reports
Related NEAT Reports
Other blog posts
posted on Jun 09, 2023 by Mike Smart
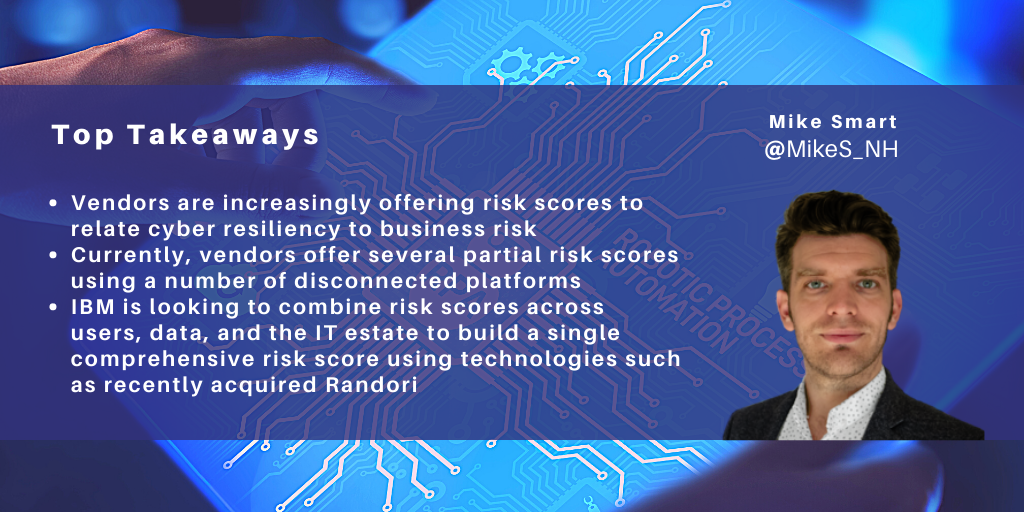
NelsonHall recently attended an IBM Security analyst day in London. This covered recent developments such as IBM’s acquisition of Polar Security on May 16th to support the monitoring of data across hybrid cloud estates, and watsonx developments to support the move away from rule-based security. However, a big focus of the event was the subject of risk.
For the last few years, the conversation around cybersecurity has shifted to risk, highlighting the potential holes within a resiliency posture, for example, and asking questions such as ‘if ransomware were to shut down operations for six hours, what would the implications for the business be?’
IBM and a number of other providers, therefore, have been offering ‘risk scores’ related to aspects of an organization’s IT estate. These include risk scores from IBM’s Risk Quantification Service, IBM Guardium, for risk related to the organization’s data, including its relationship with data security regulations; risk scores from IBM Verify related to particular users; and from recently acquired Randori, the company’s attack surface management solution.
Randori, acquired in June 2022, is a prime example of IBM’s strengths in understanding and reducing risks. Its two offerings, Randori Recon and Randori Attack, aim to discover how organizations are exposed to attackers and provide continuous automated red teaming of the organization’s assets.
After running discovered assets, shadow IT, and misconfigurations through Randori Attack’s red team playbooks, clients are presented with the risks through a patented ’Target Temptation’ model. In this way, organizations can prioritize the targets that are the most susceptible to attack and monitor the change in the level of risk on an ongoing basis.
IBM’s Risk Quantification service uses the NIST-certified FAIR model which decomposes risk into quantifiable components: the frequency at which an event is expected and the magnitude of the loss that is expected per event. In this manner, the service performs a top-level assessment of the client’s controls and vulnerabilities, makes assumptions such as the amount of sensitive information stolen during a breach based on prior examples, and produces a probability of loss and the costs related to that loss, including fines and judgments from regulatory bodies.
It is not the first time we have seen this model and a similar approach being taken by vendors offering cyber resiliency services. One such vendor is Unisys, who in 2018 offered its TrustCheck assessment, which used security data and X-Analytics' software to analyze the client's cyber risk posture and how they associate with financial impacts. These financial impacts were plotted against the threat likelihood of the event.
TrustCheck was used as a driver for the Unisys cybersecurity business; it related the expected loss against guidance to whether the value of securing the client's environment was greater than the cost to remediate a gap, and it conveyed this information to the C-level.
So what is the difference between IBM’s approach to risk and Unisys’ TrustCheck service?
IBM has been approaching its risk qualification from both ends – a bottom-up measuring of user, data, compliance, and the IT estate using platforms such as Guardium, Verify, and now Randori, and a top-down view within its Risk Quantification Service. At the analyst event in London, there was a clear indication that these risk scores would be looking to converge over time to provide a more accurate and consistent view of an organization’s risk. For example, using the outputs from Randori Recon to understand the client’s exposure; Guardium and Polar security to understand what data is being held and where it could travel; and Verify to understand what user access exists. A consistent, accurate view of the client’s resiliency would then be used to drive decision-making.
This convergence of risk scores will not be an immediate development. Randori has just undergone a year of development to integrate its UX into QRadar for a unified experience, and its upcoming development will include being brought into the IBM Security QRadar suite as part of an Attack Surface Management (ASM) service before a consistent risk score service is complete. Likewise, the acquisition of Polar Security needs time to bed in to the data security estate.
NelsonHall does, however, welcome any moves that result in more organizations knowing more about the risks to their business, and the financial risks associated, which has traditionally been a major stumbling block for organizations in understanding what remediation should be taken to increase security postures beyond the baseline of compliance requirements.
